SDK installation / package contents
This article explains how to obtain the WireSock Secure Connect SDK (WSC SDK), what files it contains, and what you typically need to integrate it into your own product.
Downloading the SDK
The SDK is published as a separate product with downloads for multiple Windows architectures (x64, x86, ARM64):
Select the appropriate package for your target architecture.
Installation and prerequisites
Administrator privileges
Installing kernel-mode drivers and running system-wide tunnel features may require Administrator privileges.
Supported architectures
The SDK is distributed for:
- Windows x64
- Windows x86
- Windows ARM64
Choose the SDK build that matches the architecture of your target machine and your application deployment.
Package contents (typical)
The exact file layout may vary by version, but a typical SDK package includes the following categories:
1) Drivers and system components
These components enable packet interception/filtering and virtual network adapter functionality.
You will typically find:
- driver files (for example,
.sys,.inf,.cat) - helper executables or installers used by the product to install/start/stop the drivers
2) Native library: wgbooster
The SDK exposes the public C API for tunnel management through the wgbooster library.
You will typically find:
wgbooster.dll(runtime library)- an import library (
.lib) for linking from C/C++ - public headers (at minimum
wgbooster.h)
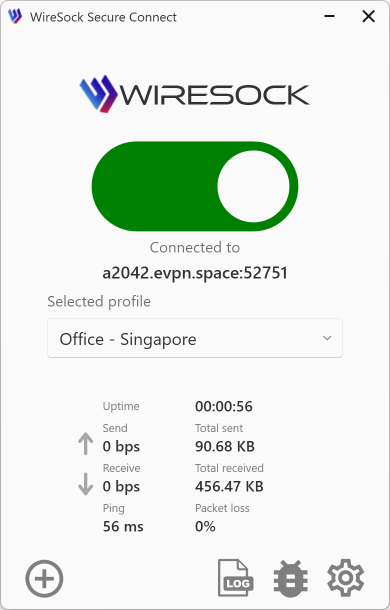
3) Reference client: wiresock-client
The SDK includes a reference implementation built on top of wgbooster.
Depending on the distribution, this may include:
wiresock-client.exe(CLI)wiresock-client-serviceWindows service components (service installation is handled by the CLI)- example configuration files or templates
For CLI usage and service mode, see:
How to integrate the SDK
Option A: Embed wgbooster into your application
This is the recommended approach if you build a custom UI and want full control over connection lifecycle and policies.
Typical steps:
- Add the SDK headers to your include path (
wgbooster.h). - Link against the import library (
wgbooster.lib) or dynamically loadwgbooster.dll. - Implement a log callback (
void (*log_printer)(const char*)) to collect library logs. - (Optional) Use the extended handle creation APIs (
*_get_handle_ex) to receive tunnel events (wg_tunnel_event). - Create and start a tunnel (for example, from a WireGuard config file).
Option B: Use wiresock-client.exe as a building block
This is useful for automation, headless deployments, and for validating that a WireGuard config works end-to-end.
Typical steps:
- Use
wiresock-client.exe importto store a configuration in a protected form (DPAPI,.dpapi). - Use
wiresock-client.exe runfor interactive use, orinstallto run as a Windows service. - Enable tunnel adapter mode with
-lacwhen required.
Configuration storage (.dpapi)
The reference client supports encrypting configuration files using Windows DPAPI and storing them with a .dpapi extension. This is intended for scenarios where configuration files should not be stored in plain text and for service-mode execution.
Troubleshooting
Network lock left enabled after a crash
If your integration uses network lock (Kill Switch) and the process terminates unexpectedly, the driver-level lock state may remain enabled.
The wgbooster API provides recovery helpers:
wg_is_network_lock_active()to detect whether lock is still activewg_reset_network_lock()to clear the driver-level lock state