Deployment Guide (Enterprise Edition)
WireSock Secure Connect provides deployment automation options designed for enterprise environments.
These options allow administrators to centrally control application behavior, restrict end-user access to specific functionality, and automate profile and license provisioning.
This guide describes supported command-line parameters, deployment modes, usage examples, and integration with Microsoft Intune, SCCM, MDT, and Group Policy (GPO).
NOTE
This section applies only to the Pro version of the application.
1. Silent Installation Requirement
For automated deployments, silent mode is mandatory.
Use the /s parameter:
/sThis ensures that the installation runs without user interaction.
2. .NET 10 Prerequisite
WireSock Secure Connect requires .NET 10 to run. Install .NET 10 before installing the application.
You can download the latest .NET 10 Desktop Runtime from Microsoft:
https://dotnet.microsoft.com/en-us/download/dotnet/10.0
Automatic .NET installation during setup
During installation, WireSock Secure Connect will automatically download and install .NET if it is not detected on the system.
To prevent the installer from installing .NET, use the following installer switch:
InstallDotNet=falseImportant: If .NET 10 is not installed, WireSock Secure Connect will not run.
3. Command-Line Deployment Parameters
Supported syntax:
wiresock-secure-connect-pro-x64-<version>.exe /s [InstallDotNet=false] Deployment=<mode> Profile=<path> License=<path>Parameters
- /s — Silent installation mode (required for automated deployment)
- InstallDotNet=false — Skip .NET installation during setup (requires .NET 10 to be installed separately)
- Deployment — Defines the user interface and feature availability mode
- Profile — Path to a profile file or directory containing profiles
- License — Path to a license file
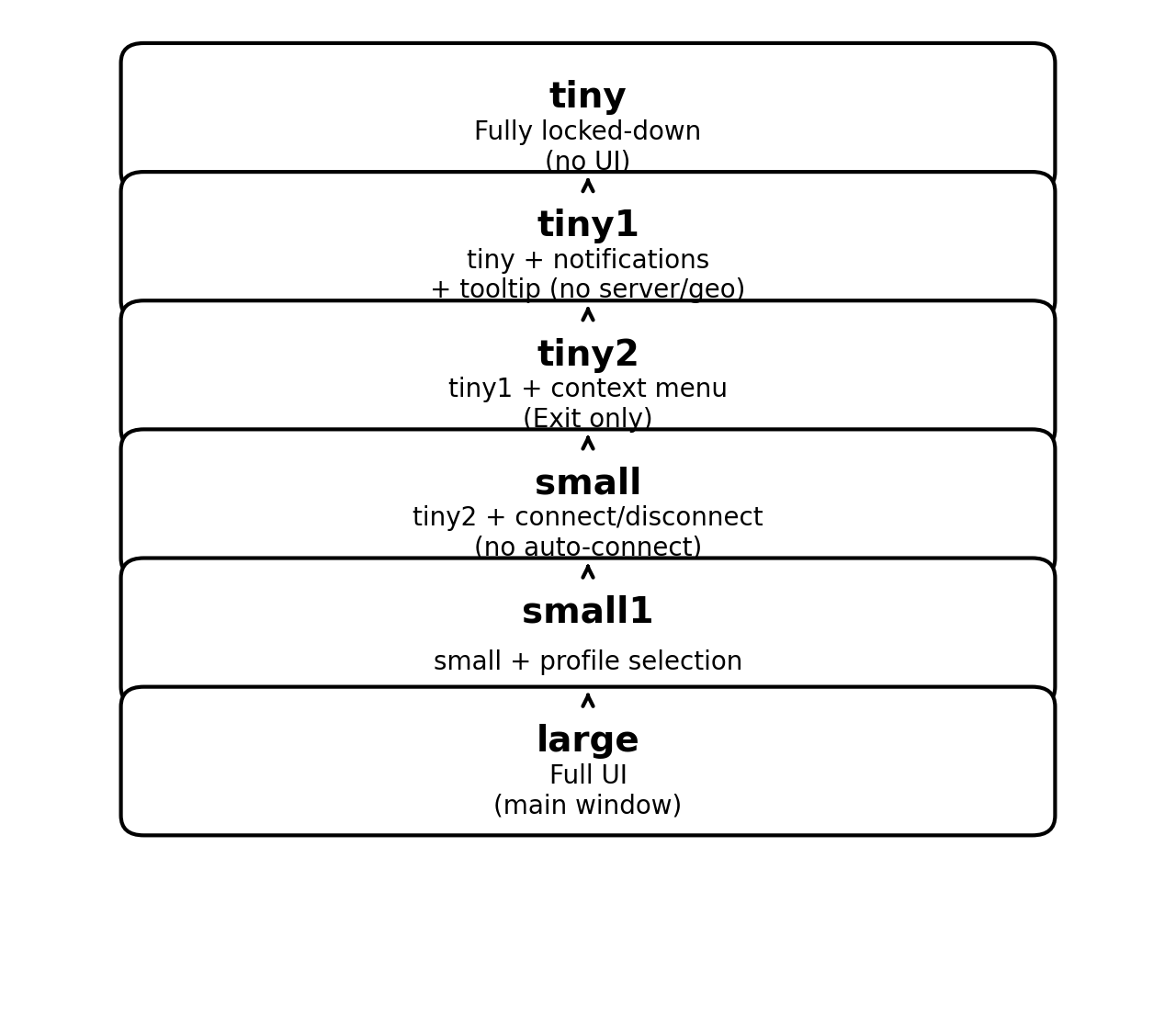
4. Deployment Modes
The Deployment parameter limits the functionality available to end users.
Mode Comparison Table
| Mode | Auto start | Auto connect | System tray icon | Notifications | Context menu | Connect/Disconnect | Profile selection | Main window |
|---|---|---|---|---|---|---|---|---|
| tiny | Yes | Yes | Status only | No | No | No | No | No |
| tiny1 | Yes | Yes | Yes | Yes | No | No | No | No |
| tiny2 | Yes | Yes | Yes | Yes | Exit only | No | No | No |
| small | Yes | No | Yes | Yes | Yes | Yes | No | No |
| small1 | Yes | No | Yes | Yes | Yes | Yes | Yes | No |
| large | Yes | No | Yes | Yes | Yes | Yes | Yes | Yes |
Deployment Modes Diagram
5. Profile Parameter
Profile=<full_path_to_profile_or_directory>- Accepts a single profile file or a directory containing multiple profiles.
- Profiles are automatically deployed and stored in encrypted form.
- In restricted modes (
tiny,tiny1,tiny2,small), deploying a single profile is recommended.
6. License Parameter
License=<full_path_to_license_file>- The license file may contain multiple licenses.
- Licenses must be separated by an empty line.
- The base license must appear before overlays.
- Recommended: use the license file downloaded from your account dashboard.
7. Deployment Examples
Example 1 — Fully Locked-Down Corporate Deployment
wiresock-secure-connect-pro-x64-3.3.3.1.exe /s Deployment=tiny Profile=C:\deploy\corp.conf License=C:\deploy\license.txtExample 2 — Controlled Deployment with Manual Connect
wiresock-secure-connect-pro-x64-3.3.3.1.exe /s Deployment=small Profile=C:\deploy\profiles\ License=C:\deploy\license.txtExample 3 — Full UI Deployment
wiresock-secure-connect-pro-x64-3.3.3.1.exe /s Deployment=large Profile=C:\deploy\profiles\ License=C:\deploy\license.txt8. Microsoft Intune Deployment
WireSock Secure Connect can be deployed using Microsoft Intune as a Win32 application.
High-level steps
- Package the installer using the Microsoft Win32 Content Prep Tool.
- Use an install command that includes
/sand the desired parameters. - Configure detection rules (for example, a registry key or installed executable).
- Assign the application to device or user groups.
9. SCCM Deployment
For Microsoft Configuration Manager (SCCM):
- Create a new Application.
- Specify the install command (example):
wiresock-secure-connect-pro-x64-3.3.3.1.exe /s Deployment=tiny Profile=\\fileserver\deploy\corp.conf License=\\fileserver\deploy\license.txt- Configure a detection method (for example, file version or registry).
- Deploy to collections.
10. MDT Deployment
For Microsoft Deployment Toolkit (MDT):
- Add the installer to your Applications.
- Use a silent install command with
/s. - Add the application to the Task Sequence.
- Ensure profiles and licenses are accessible during deployment (local media or a reachable network share).
12. Silent Upgrade
Upgrading can be performed by running the new installer version with /s.
The installer performs an in-place upgrade while preserving profiles and licenses.
Example:
wiresock-secure-connect-pro-x64-3.4.0.exe /s Deployment=tiny13. Logging and Troubleshooting (Silent Install)
Silent deployments typically fail due to environmental issues (permissions, blocked driver binaries, disabled Windows services, or security software). Use the checklist below to diagnose quickly.
13.1 Collect installer logs
- Check %TMP% for installer logs that start with WireSock (for example,
WireSock*.log). - If the installation includes a kernel driver, the driver installer may generate a separate driver log file. Include it when reporting issues.
13.2 Validate prerequisites and environment
- Ensure the installer is executed with sufficient permissions (enterprise deployments usually run under SYSTEM).
- Verify required Windows services are running (commonly involved):
- Plug and Play
- Windows Management Instrumentation (Winmgmt)
- Cryptographic Services (CryptSvc)
13.3 Check security software (common cause)
Some antivirus/EDR products may quarantine or block driver files immediately after extraction.
- Review antivirus/EDR logs for blocked items (for example, the driver file
ndiswgc.sys, if applicable). - If this is confirmed as a false positive, consider a controlled workaround:
- temporary exclusion for the installer and driver files during deployment, or
- a short-lived maintenance window policy exception
13.4 Confirm network access (for profile/license delivery)
If Profile= or License= points to a network share, ensure the deployment context (SYSTEM/user) can reach that path.
- Prefer local staging (copy files locally first) when deploying through Intune/SCCM/MDT.
- If using UNC paths, validate permissions explicitly for the deployment identity.
13.5 Capture exit code (recommended)
When deploying via scripts, capture the installer exit code and log it centrally. This helps correlate failure causes across the fleet.
14. Known Issues
Antivirus/EDR may block driver files
Some security products can quarantine or block kernel driver binaries immediately after extraction (for example, ndiswgc.sys, if applicable).
If installation fails, review antivirus/EDR logs and consider deploying an exclusion or temporary policy exception in a controlled manner.
Installation may fail if required Windows services are disabled
If any of the following services are disabled, driver installation and system integration may fail:
- Plug and Play
- Windows Management Instrumentation (Winmgmt)
- Cryptographic Services (CryptSvc)
Network share access in SYSTEM context
When deploying via Intune/SCCM/MDT, the installer often runs under the SYSTEM account.
UNC paths for Profile= and License= may not be accessible in that context. Prefer staging files locally or explicitly granting access to the deployment identity.
.NET 10 is required at runtime
If .NET 10 is not installed, WireSock Secure Connect will not run. If you use InstallDotNet=false, ensure .NET 10 is deployed separately.
15. Best Practices
- Always use
/sin automated environments. - Test deployment modes in a staging ring before mass rollout.
- Use
tinyfor fully managed endpoints; usesmall/small1when limited user interaction is required. - Store profile and license files securely.
- Validate antivirus/EDR compatibility before mass deployment.
For enterprise deployment assistance, contact WireSock support.
16. Winget Deployment
WireSock Secure Connect is available via Windows Package Manager (winget) under the following ID:
NTKERNEL.WireSockVPNClientWinget can be used for installation, upgrade, and removal scenarios.
For enterprise deployments, it is recommended to combine winget with a configuration staging mechanism (Intune, SCCM, MDT, or scripts).
16.1 Basic Installation
winget install --id NTKERNEL.WireSockVPNClient --exact --silent--exactensures the correct package is selected.--silenttriggers silent installation (if defined in the manifest).
16.2 Installation with Deployment Parameters
To pass installer parameters (such as /s, Deployment=, Profile=, License=, or InstallDotNet=false), use the --override switch:
winget install `
--id NTKERNEL.WireSockVPNClient `
--exact `
--silent `
--override "/s Deployment=tiny Profile=C:\ProgramData\WireSock\corp.conf License=C:\ProgramData\WireSock\license.txt"Ensure that profile and license files exist on the system before running the command.
If .NET is pre-installed and should not be installed automatically:
--override "/s InstallDotNet=false Deployment=tiny"16.3 Recommended Enterprise Pattern
Winget does not deploy configuration files automatically.
Use a two-step deployment approach:
Step 1 — Stage configuration files
New-Item -ItemType Directory -Force -Path "C:\ProgramData\WireSock"
Copy-Item "\\fileserver\deploy\corp.conf" "C:\ProgramData\WireSock\corp.conf"
Copy-Item "\\fileserver\deploy\license.txt" "C:\ProgramData\WireSock\license.txt"When deploying via Intune or SCCM, installation typically runs under the SYSTEM account.
Ensure the SYSTEM account has access to network paths or stage files locally first.
Step 2 — Install via winget
winget install `
--id NTKERNEL.WireSockVPNClient `
--exact `
--silent `
--override "/s Deployment=tiny Profile=C:\ProgramData\WireSock\corp.conf License=C:\ProgramData\WireSock\license.txt"16.4 Upgrade via winget
winget upgrade --id NTKERNEL.WireSockVPNClient --exact --silentTo preserve a specific deployment mode:
winget upgrade `
--id NTKERNEL.WireSockVPNClient `
--exact `
--silent `
--override "/s Deployment=tiny"16.5 Uninstall via winget
winget uninstall --id NTKERNEL.WireSockVPNClient --exact --silent16.6 Limitations of Winget Deployment
- Winget does not automatically distribute profile or license files.
- UNC paths may not be accessible in SYSTEM context.
- Installer arguments rely on correct manifest behavior.
- Compliance reporting may be limited compared to Intune/SCCM Win32 applications.
Winget is well suited for automated upgrades and lightweight rollout scenarios.
For fully controlled enterprise deployments (application + configuration in one package), consider Intune Win32, SCCM, or MDT-based distribution.